Immune Intelligence: Rebuilding Morocco’s Security Services Like the Human Body
Morocco’s security architecture should not be built by imitating the CIA, Mossad or DGSE. A model inspired by the human immune system offers a faster, cheaper and more resilient alternative.
Immune Intelligence: Rebuilding Morocco's Security Services Like the Human Body — Theory, Roadmap, and a Real Crisis Example
Executive Summary
Morocco already possesses every organ of a world-class security system: barrier forces at every frontier, Moqaddems and Forces Auxiliaires embedded in every neighbourhood and souk, a vast administrative data apparatus across all Amalat and ministries, and elite analytical units in the DGST, DGED and BCIJ.
What is missing is the wiring that turns these organs into one living immune system.
This proposal reconnects them — without dissolving any service, without creating new ministries, and while preserving full central veto and strategic authority.
The result: 10× faster response on routine threats, perfect institutional memory, controlled surges, and zero tolerance for conceptzia — all while protecting the core assets that will host the 2030 World Cup.
In earlier posts on this site I mapped the architectural blind spots in Morocco's current security setup and showed why simply copying the organisational pyramids of the CIA, Mossad, DGSE or FSB keeps producing the same grotesque failures — despite all of them containing genuinely talented people. The 1973 Yom Kippur War caught Israeli intelligence flat-footed even though they had the Egyptian war plans on file. The CIA missed Pakistan's nuclear programme for years. French intelligence lost its grip across the Sahel despite decades of presence. The FSB miscalculated catastrophically in Ukraine. And on October 7, 2023, Shin Bet and IDF intelligence dismissed the exact Hamas attack blueprint that had been circulating for over a year.
These are not failures of talent. They are failures of architecture.
Readers and professionals inside Morocco's system have asked the only question that matters: "What should we do instead?"
Here is the complete answer. It is not another imported model. It is a practical, biology-inspired operating system that Morocco can implement without dissolving any existing service. It is cheaper, faster to build, and far more resilient than any imported bureaucracy. I call it Immune Intelligence.
1. The Human Body's Defenses — What 3.8 Billion Years of Evolution Actually Built
The human body does not rely on a single "super-agency" sitting in a capital and issuing orders to everyone. If it did, you would die of a common cold while waiting for the paperwork to clear. Instead, it has built a five-layer defence system that works automatically, around the clock, and has kept our species alive for 300,000 years through plagues, parasites, venoms, and threats no one predicted in advance.
Here is exactly how it works — not in medical jargon, but in the operational logic that matters for what comes next.
Layer 1 — Physical and chemical barriers: the perimeter that never sleeps
Your skin is the largest organ in the body, and its primary job is the simplest one: stop anything from getting in. Mucous membranes line your nose, throat, and lungs and trap particles before they reach deeper tissue. Tears wash your eyes. Saliva contains enzymes that dissolve bacteria. Stomach acid — powerful enough to corrode metal — destroys nearly everything you swallow that does not belong there. Tiny hairs called cilia in your airways sweep debris upward and outward before foreign particles can settle.
None of these barriers are intelligent. They do not analyse the threat. They simply block entry. They cost the body almost nothing to maintain once built, and they stop the overwhelming majority of threats before any fight even begins. Morocco already understands this principle instinctively: the coast guard patrols off Tanger Med, the border gendarmerie along the eastern and southern frontiers, customs screening at Mohammed V and Marrakesh Menara airports, DGSSI firewalls on critical digital infrastructure — all of these are barrier-layer defences. They operate continuously, they require no strategic decision-making in the moment, and they stop most threats before anyone at the centre needs to be informed. But when they are breached — a forged document that passes customs, an operative who crosses an unmonitored stretch of frontier, a cyber intrusion that slips past the firewall — everything that follows depends on the layers below.
Layer 2 — Innate rapid-response teams: the coast guard that intercepts first under standing orders
The moment something foreign crosses the barrier, specialised cells are already waiting: neutrophils (the fastest, most aggressive first responders), macrophages (larger cells that literally engulf and isolate invaders), natural killer cells (which detect and destroy compromised body cells before they spread infection), and complement proteins (chemical agents that punch holes in bacterial membranes).
These teams have one critical characteristic: they do not need to identify the enemy precisely before acting. They recognise general threat patterns — "this organism carries a bacterial cell wall," "this cell is behaving abnormally" — and they move to contain and neutralise immediately.
Consider a concrete Moroccan parallel. A Royal Navy coast guard vessel patrolling off the strait of Gibraltar detects an unidentified boat approaching Tanger Med at 2 a.m. — no transponder, no lights, erratic course. The vessel does not radio Rabat and wait for a committee to determine whether this is a fishing boat, a smuggling operation, or something worse. Under standing rules of engagement approved centrally long before the incident, the coast guard intercepts, contains, and identifies. If it is a lost fisherman, the encounter ends with assistance and a report. If it is a smuggling vessel, detention and escalation follow. The critical point: the authority to act was pre-authorised by the centre; the decision to act in this specific moment belongs to the local commander.
This is exactly how the innate immune system operates. It does not freelance. It follows broad, pre-established rules: surround anything that does not belong, isolate it, and neutralise it if it resists. No request for permission. No chain of approvals. The centre defined the rules; the periphery executes them in real time.
This layer handles roughly 99 % of all threats the body ever faces. The vast majority of infections are detected, contained, and destroyed locally, within hours, by teams operating under pre-authorised protocols. The adaptive immune system — headquarters — never even learns about most of these encounters because they never escalated beyond local containment.
The cost of this speed is imprecision. Innate responders cause some collateral damage: they destroy some healthy cells in the vicinity, they trigger local inflammation, they are not surgical. But the body accepts that trade-off because the alternative — waiting for a perfectly targeted response — gives the enemy hours or days to multiply, spread, and potentially overwhelm the host.
The peripheral nervous system: the sensors that read the environment before any threat declares itself
The immune system does not operate blind. It is wired into the body's vast peripheral nervous system — millions of nerve endings embedded in every tissue, every surface, every organ. These nerve endings do not fight threats. They sense the environment continuously. They detect temperature shifts, pressure changes, chemical imbalances, the difference between a familiar texture and something that should not be there. They are the body's first source of information about what is happening at the local level, and they feed that information upward — through the spinal cord to the brain — with extraordinary speed.
Morocco has an exact equivalent, and it is one of the oldest and most distinctive features of the Makhzen's architecture: the Moqaddem (المقدم) and the Cheikh (الشيخ). These are not police officers. They are not intelligence agents. They are community-embedded sensors — assigned to specific neighbourhoods, streets, and rural areas, reporting through the local authority chain (caïd, pacha, amil, wali). Historically, a good Moqaddem knew his street the way a nerve ending knows its tissue: intimately, continuously, personally. He walked his area daily, spoke with merchants, noted who was new, who had left, whose behaviour had shifted, what tensions were building. He was the starting point for identity vetting — long before any carte d'identité nationale existed, the Moqaddem was the knowledge system. A Cheikh in a rural commune served the same function across wider terrain: the human sensor who read the environment and reported upward.
This system still functions. Moqaddems and Cheikhs still exist in every neighbourhood and commune, still report to local authorities, still perform administrative tasks including identity verification and local mediation. But the sensory acuity has diminished — and with it, the integrity of a chain that depends entirely on their vigilance. The Moqaddem's certificat de résidence or rather the *enquiry" document (البحث) done by the Moqaddem is the foundational document in Morocco's entire identity verification architecture. Without it, a regular citizen cannot obtain a carte d'identité nationale. The Moqaddem was designed to issue this certificate based on personal knowledge of the applicant's actual residence — verified through his own daily presence in the neighbourhood, not through checking pre-existing documents. When a younger generation of Moqaddems relies on the CIN to verify residence rather than independently confirming it through firsthand knowledge, the system becomes circular: the document that was supposed to ground-truth identity now depends on other documents for its own validation. The foundation verifies nothing.
The older generation took pride in the role and cultivated deep, personal knowledge of their constituency. The younger generation is genuinely better educated — many hold the baccalauréat or higher — and this is an asset, not a weakness. But education brings awareness of the social stigma that has attached itself to the Moqaddem's function. The role is traditionally associated with surveillance, with snooping, with being the Makhzen's eyes in the neighbourhood. For the older generation, this carried authority and a sense of public service. For a younger, educated cohort that compares itself to police officers or civil servants in other ministries, the stigma is something to distance themselves from. And the most natural way to create that distance is to stop doing precisely the activities that carry the stigma: the daily walking tour, the personal inquiries, the visible presence in every street and shop, the knowing-everyone's-business that made the Moqaddem irreplaceable as a sensor. The result is a rational response to low prestige that quietly undermines the most valuable dimension of the job. The daily walking tour of the street — the continuous environmental read — has become less systematic, less thorough. The nerve endings are still anatomically present, but they have lost sensitivity. In medical terms, this is peripheral neuropathy: the gradual degradation of sensory nerve function, where the body progressively loses its ability to feel what is happening at the surface. A patient with neuropathy in the feet can still walk, still function, still appear healthy — but can no longer detect the small cut, the pressure sore, the infection building silently under the skin. By the time the problem becomes visible, it may require drastic intervention.
Restoring the Moqaddem's sensory function therefore requires more than training and digital tools — it requires revaluing the role itself. How to give prestige and institutional recognition to a function that is inherently about local knowledge and community proximity is a serious policy challenge that this proposal names but does not pretend to solve in full. What it does provide is the architectural reason why solving it matters: without functioning peripheral nerves, the most brilliant brain in the world is blind.
Alongside the Moqaddems, Morocco possesses another embedded sensory force that is even more visibly present and even more underutilised for intelligence purposes: the Forces Auxiliaires. These paramilitary units are everywhere — in city streets during daily life, at social and religious events, in rural souks, at the entrances of hospitals and government buildings, in remote areas where gendarmerie and police appear only when trouble has already erupted. They are in continuous, daily contact with the population at a level of proximity that no other security force matches. They know the local terrain, the rhythms of their assigned area, the faces that belong and the faces that do not. They report through the local authority chain (caïd, pacha, amil, wali) and, where applicable, their institutional headquarters.
In biological terms, the Forces Auxiliaires are tissue-resident macrophages — immune cells that live permanently embedded in specific tissues (skin, lungs, liver, gut) rather than circulating from a central base. These cells do not wait for an infection to be reported to them. They are already there. They are the first to detect a change in the local environment, and in a properly wired immune system, they are the first to respond and the first to relay information to the broader network.
The leadership of the Forces Auxiliaires is highly educated. Even the lower echelons now hold baccalauréat-level qualifications if not higher. Their institutional potential — comparable, with appropriate training and mandate, to Spain's Guardia Civil in terms of territorial coverage and dual security-intelligence function — is enormous. Yet they are currently positioned below regular police in institutional prestige. The Forces Auxiliaires do gather intelligence — their military affiliation means that some of what they observe reaches military intelligence through their institutional chain, and some flows back to the Amalat and Wilayat through local authority channels. But the quantity, quality, and systematic channelling of this information remain opaque. How much of it is captured in a form that allows analytical cross-referencing? How much reaches the DGST or DGED analytical pipelines? How much is valued and acted upon versus filed and forgotten? These are questions without clear public answers — and the absence of clear answers is itself the diagnostic. In a properly wired immune system, every tissue-resident macrophage's detection of an anomaly reaches the analytical centres through a defined, auditable pathway. The Forces Auxiliaires' daily observations — the unusual vehicle parked near a critical site, the cluster of unfamiliar faces in a neighbourhood, the merchant whose business pattern has changed — represent an intelligence stream of potentially enormous value that is not systematically integrated into the national analytical architecture.
The lymphatic network: the administrative apparatus that collects data it never analyses
The body possesses one more system that is rarely discussed but essential to immune function: the lymphatic network. This is not the blood supply (the main command and logistics channel) and not the nervous system (the sensory network). It is a secondary drainage and surveillance system that runs quietly through every tissue, collecting fluid, cellular debris, and — critically — samples of everything the tissue has been exposed to. This material is filtered through lymph nodes, where immune cells examine it. Most of what the lymphatic system collects is mundane, routine, unremarkable. But occasionally it carries the first molecular trace of a cancer cell, a hidden infection, or a toxin that the primary sensory and immune systems missed entirely.
Morocco's lymphatic network is its vast administrative apparatus: the Amalat (عمالات), Wilayat (ولايات), Caïdat (قيادات), Pachalat (باشويات), and the regional offices of every ministry — health, education, commerce, agriculture, housing, transport. These institutions collect enormous quantities of data about the population as a routine byproduct of their administrative function: land transactions, business registrations, school enrolments, health clinic visits, water and electricity consumption patterns, market licence applications, building permits, rental contracts. Individually, none of this constitutes intelligence. Collectively, cross-referenced and filtered through an analytical node, it becomes precisely the kind of ambient environmental data that reveals anomalies invisible to conventional surveillance: a neighbourhood where electricity consumption spikes unexpectedly, a cluster of new business registrations by individuals with no local history, unusual rental activity near a critical site, a health clinic reporting an atypical pattern of chemical exposure.
Today, virtually none of this administrative data reaches the intelligence architecture. It fulfils its bureaucratic purpose and sits in ministry silos, unconnected to any analytical system. The lymphatic network is present and functioning — but it drains without ever filtering. The immune system never sees what it collects.
Why this matters: the body has all the same organs Morocco has — but better wiring
Here is the decisive point, and it must be stated with absolute clarity because it is the answer to anyone who reads this post and says "we already have all of this."
Morocco already possesses barrier forces (coast guard, border gendarmerie, customs, DGSSI). Morocco already possesses distributed sensors embedded in every community (Moqaddems, Cheikhs, Forces Auxiliaires). Morocco already possesses a specialist analytical elite (DGST, DGED, BCIJ). Morocco already possesses a vast administrative data-collection apparatus (Amalat, Wilayat, ministry offices). Morocco already possesses central coordination at the highest level.
What Morocco does not possess is the wiring that connects these assets into a single functioning immune system.
The Moqaddem's observation about a change in his street does not reach an analytical node, or not always. The Forces Auxiliaires agent's awareness of unfamiliar faces near a hotel does not enter a threat-assessment database. The Amala's records of unusual business registrations are not cross-referenced with DGST surveillance data. The health ministry's report of atypical clinic visits is not linked to the OSINT layer's detection of anomalous water deliveries.
The human body does not have better organs than Morocco has forces. The human body has better wiring. Every nerve ending, every tissue-resident macrophage, every lymph node is connected — through the nervous system, through the circulatory system, through the lymphatic network — into a single integrated architecture where information flows from the periphery to the analytical centres and back in seconds, not days. The Moqaddem is the nerve ending. The Forces Auxiliaires agent is the tissue-resident macrophage. The administrative apparatus is the lymphatic network. The DGST analyst is the adaptive immune cell. The Palace is the brain.
All of the components exist. The wiring between them is what this proposal builds where it does not yet exist, and upgrades where it does.
Layer 3 — Inflammatory and systemic alarms: the tools that look like they are hurting you but are actually saving your life
This is the layer most people misunderstand, and it is the most important one for our purposes.
When the innate teams are fighting a serious infection, they release chemical messengers called cytokines. These trigger a cascade of responses that feel terrible but are deliberately engineered for survival:
Fever. Your body raises its own temperature, sometimes to dangerous levels. This is not a malfunction. Most pathogens reproduce optimally at normal body temperature; raising it by even 1–2 degrees slows their replication dramatically while the immune system catches up.
Vomiting and diarrhoea — forced expulsion of compromised elements. The body's most aggressive purge mechanisms exist for one purpose: to forcibly eject a contaminant that cannot be neutralised in place, accepting the short-term cost of disruption because the alternative is systemic poisoning. The body does not attempt to negotiate with a toxin in the gut; it empties the gut entirely, violently, immediately. In security terms, this is the logic behind declaring a compromised foreign diplomat persona non grata and expelling them within 48 hours, before they can activate deeper networks — even though the expulsion damages the diplomatic relationship and alerts the adversary. Or consider a compromised secure communications channel: the channel is shut down entirely and replaced, even though this disrupts ongoing operations, because keeping it open means the adversary reads everything. The cost of the purge is real and visible. The cost of inaction — letting the contamination remain inside the system — is catastrophic and often invisible until it is too late.
Pain. Pain is not mere suffering — it is the body's most sophisticated graduated alert and behaviour-modification system. Mild pain at a wound site communicates "protect this area and limit its use." Intense pain communicates "cease all activity, immobilise the affected region, and seek external assistance immediately." The body calibrates pain intensity to threat severity, and — critically — pain does not merely inform, it compels behavioural change. You cannot simply acknowledge pain and continue as before; it forces a shift in priorities whether you welcome it or not. In security terms, this is the difference between an intelligence brief that sits in a minister's inbox (information) and a graded national alert protocol that automatically redirects resources, restricts access to vulnerable sites, and compels decision-makers to convene (behavioural override). The body's pain system ensures that threats above a certain severity cannot be filed away and forgotten — they demand action by design.
The body deliberately accepts all of this short-term damage — the energy cost of fever, the disruption of purging, the immobilisation of pain — because the alternative is death. This is the principle that every security architect must internalise: a system that optimises for zero discomfort will eventually optimise itself into catastrophic failure. The body never makes that mistake. It optimises for survival probability, not comfort.
Layer 4 — Adaptive targeted immunity: the detective unit that never forgets a face
Now we arrive at the layer that separates the human immune system from every other defence system in nature.
B-cells and T-cells are specialist units. Unlike the innate responders, they do need to know the enemy's exact identity. The first time they encounter a novel pathogen, the response is slow — days, sometimes weeks — because they must design a perfectly tailored weapon (an antibody) that fits the specific threat like a key fits a lock.
But here is the revolutionary part: once they have solved that puzzle, they create memory cells. These memory cells live for decades — sometimes for life. The next time the same pathogen appears, the adaptive system recognises it instantly and produces antibodies in hours instead of weeks. The response is faster, stronger, and more precise than the first time.
This is exactly what vaccines exploit. A vaccine introduces a harmless fragment of a pathogen — just enough for the adaptive system to study, build antibodies, and create memory cells — without ever causing the actual disease. When the real pathogen arrives later, the body already has the case file and the weapons ready.
The distinction between Layer 2 and Layer 4 is the foundation of everything that follows, so let me state it one more time in operational terms. Innate response is the coast guard vessel that intercepts and contains an unidentified threat under standing orders — fast, broad, effective against 99 % of incursions. Adaptive response is the BCIJ investigative team that spends weeks building a complete dossier on a specific terrorist cell, then archives that dossier permanently so the next encounter with the same network is resolved in hours instead of months. Both are essential. Neither can replace the other. A country that has only rapid containment will handle routine threats but be helpless against a sophisticated, evolving adversary. A country that has only specialist investigators will dismantle yesterday's cell brilliantly while today's attack unfolds unopposed.
Layer 5 — Regulatory mechanisms and self/non-self discrimination: the internal affairs unit that prevents civil war
This is the layer the body cannot survive without, yet it is the one most often ignored in security discussions.
The immune system is extraordinarily powerful — powerful enough to destroy every tissue in the body if it turns inward. Regulatory T-cells exist to prevent exactly that. They patrol the system, suppress overreaction, and enforce one absolute rule: never attack self. The body distinguishes its own cells from foreign invaders using identity markers called MHC molecules, displayed on every cell surface — essentially an internal passport that is continuously checked, not just at the border but inside every tissue, at every moment. Any cell that cannot present the correct marker is treated as hostile, regardless of where it is found or how familiar it appears. In security terms, this is the principle of zero-trust credentialing applied not only to digital systems but to every human element of the architecture: every officer, every agent, every administrative node carries a continuously verified authentication — and the system treats anything without valid credentials as potentially compromised, no matter how long it has been inside.
When this discrimination mechanism fails, the result is autoimmune disease: the body destroys its own joints (rheumatoid arthritis), its own nerves (multiple sclerosis), its own insulin-producing cells (Type 1 diabetes). These diseases are often more devastating than any external infection. Morocco's security history — and the history of every intelligence service — contains examples of exactly this pathology: loyal officers purged during internal paranoia, constructive analysts silenced because their warnings were mistaken for disloyalty, entire networks dismantled because the system could not distinguish a legitimate internal critic from a foreign-directed threat. The immune model places the self/non-self discrimination function exclusively at the centre — the Palace as regulatory T-cell — because this decision is too consequential and too prone to error to be delegated to the periphery.
There is one more biological concept that must be grasped: the microbiome. The body hosts trillions of bacteria in the gut, on the skin, in the respiratory tract — organisms that are technically "foreign" but are essential allies. They help digest food, produce vitamins, train the immune system, and even fight off hostile bacteria. The body has learned not to attack them. In Morocco's security architecture, the microbiome includes trusted private-sector partners who provide commercial intelligence, academic researchers whose open-source analysis feeds strategic thinking, allied foreign intelligence services whose liaison channels deliver critical data, and — increasingly — diaspora networks whose knowledge of foreign environments is irreplaceable. These actors are not "inside" the agency, but the system depends on them. A healthy immune system protects its microbiome; a paranoid one destroys it and weakens itself in the process.
And finally: apoptosis — programmed cell death. When a cell is infected beyond recovery, or when it has been compromised and might spread damage to surrounding tissue, the body orders it to self-destruct cleanly. The cell dies quietly, is absorbed by neighbouring cells, and the system continues without disruption. This is not punishment — it is protection of the network. In security terms: when an officer or unit is confirmed compromised — turned by a foreign service, corrupted, or operationally burned beyond recovery — the system must have a codified, humane, professional exit protocol. The individual is removed cleanly, debriefed thoroughly, given a dignified transition, and the network around them is preserved intact. The contrast is with the two pathological alternatives that plague most intelligence services: noisy purges that destroy morale and expose operational details (autoimmune overreaction), or quiet cover-ups that leave the compromised element in place to spread damage further (untreated infection). Apoptosis is neither. It is precise, quiet, and final — and the system is stronger afterward because the vulnerability has been excised without collateral destruction.
2. The Same System Through an Engineer's Eyes
Everything above is biology. Now forget every medical word and look at it purely as a systems engineer designing the most resilient possible control architecture for a complex, constantly threatened organisation. This is one of the most successful control systems ever built — and it was built not by any genius designer, but by 3.8 billion years of relentless testing where every failure meant death.
Here is what the engineer sees:
Perimeter firewall and intrusion-prevention system (skin, mucosa, acid). Cheap to build, cheap to maintain, always running. It does not think. It blocks. If it fails at one point, the breach is detected by the next layer within seconds. Every building has walls and locked doors for the same reason — not because walls are clever, but because they stop 90 % of threats before you ever need a guard.
Distributed autonomous sensors and first responders (innate cells). Stationed everywhere, not concentrated at headquarters. They act on local authority, within seconds, using simple rules: "If it looks foreign, contain it. If it resists, destroy it. If it is bigger than you can handle, call for backup." They do not send a report to the capital and wait for instructions. The critical engineering insight: the cost of a false positive (killing a few healthy cells) is trivial compared to the cost of a false negative (letting an infection spread for hours while waiting for confirmation from above).
Real-time alarm and escalation system (cytokines, inflammation). Like the alarm network in an industrial plant — not the kind of alarm that just blinks a light on a dashboard, but the kind that automatically triggers emergency procedures. Sprinklers go on. Ventilation shuts down. Emergency teams are dispatched. The alarm does things, it does not merely inform. And the system has different alarm levels: local inflammation for a minor breach, systemic fever for a serious invasion.
Emergency overclocking protocol (fever). The body deliberately runs itself above normal operating parameters for a limited period. This is expensive — fever burns enormous energy, stresses organs, and cannot be sustained indefinitely. But it buys time for the precision systems to spin up. Every engineer recognises this trade-off: you push the machine past rated capacity during an emergency, knowing it will cost you maintenance later, because the alternative is total system failure right now.
Emergency purge mechanisms (expulsion of compromised elements). When contamination has entered the system and cannot be neutralised in place, the fastest solution is to flush the entire affected section. An oil refinery vents contaminated fuel rather than letting it reach the refinery core. A data centre dumps a compromised server rather than letting malware spread laterally. The body does the same thing — violently, immediately, effectively.
Behavioural override system (pain). Pain does not just signal damage — it compels behavioural change. It forces the organism to stop using the damaged limb, to rest, to seek help. The critical engineering distinction: an alert that merely informs (a status light on a dashboard) is functionally useless if the operator can ignore it. An alert that automatically redirects resources, restricts access to the damaged zone, and forces the operator to respond — whether convenient or not — saves the system. Pain is the body's mandatory-response protocol. It cannot be filed away for later review.
Learning engine with permanent memory (adaptive immunity). This is where the body outperforms every human-designed security system in history. It learns the exact signature of every threat it survives, stores that signature permanently, and uses it to respond ten times faster the next time. No human organisation does this reliably. The CIA had the 1973 Egyptian attack plans and failed to act on them. Shin Bet had the October 7 blueprint and filed it away. The body never makes that mistake — because the memory is built into the architecture, not dependent on whether an analyst remembers to read last year's report.
Self/non-self identity verification (MHC system). Every cell carries an identity badge. Anything without the right badge gets destroyed. Anything with the badge is protected. The engineering equivalent: zero-trust security architecture where every device on the network must continuously authenticate, and any device that fails authentication is immediately isolated.
Central resource governor (the hypothalamus and metabolic regulation). There is a central coordinator — but it does not micromanage daily operations. It answers only the biggest questions: "Is this threat existential? How much energy can the system safely burn? Which non-critical processes can be temporarily shut down? When must we de-escalate to prevent burnout?" It is the CFO and the chairman of the board, not the plant manager.
One honest limitation the engineer must acknowledge: the immune system was not designed from a blueprint. It evolved through billions of generations of organisms that lived and died, with every failure ruthlessly eliminated. Morocco cannot afford billions of trial runs. But that is precisely why the architecture must be made explicit — written down, tested through simulation, and refined deliberately — rather than left to evolve through real catastrophes. We are copying the blueprint that evolution already perfected. We are just skipping the 3.8 billion years of fatal mistakes.
3. Abstract Levels of Organisation — The Slide for the Decision-Maker
Remove the cells. Remove the engineering jargon. Four clean tiers remain, and each one maps directly to structures that already exist in Morocco — or should.
Tier 0 — Core Asset Protection: What Must Survive at All Costs
In the body: the genome (the complete set of genetic instructions) and the ability to reproduce. Everything else — muscles, skin, even limbs — can be sacrificed if the core survives.
In Morocco: sovereignty, the monarchy as the stabilising institution, critical infrastructure (ports, power plants, water systems, the new high-speed rail network, and the 2030 World Cup venues), population cohesion, and international reputation. These are the organs the system exists to protect. Everything else is peripheral.
Tier 1 — Passive and Preventive: Barriers
In the body: skin, mucosa, acid, cilia.
In Morocco: border surveillance systems, port and airport screening, visa controls, physical perimeter security at critical sites, and — increasingly — the digital perimeter (firewalls, DGSSI cyber defences). These cost relatively little to maintain once built, they operate continuously, and they stop most threats before any human decision-maker needs to be involved. Morocco already has most of these; the question is integration and completeness, not invention.
Tier 2 — Innate Rapid and General: Distributed First Responders
In the body: macrophages, neutrophils, NK cells.
In Morocco: regional DGSN units, local gendarmerie posts, and frontline DGST personnel stationed across the country. These are the people who encounter threats first. In the current system, they often detect the threat but must wait for central approval before acting decisively. In the immune model, they are empowered to contain and neutralise clear threats immediately using pre-defined rules of engagement — exactly as a macrophage destroys a bacterium without consulting the spleen.
Tier 3 — Adaptive Precision and Memory: Specialist Corps
In the body: B-cells, T-cells, antibodies, memory cells.
In Morocco: the BCIJ (specialised counter-terrorism and organised crime), elite DGST analytical cells, DGED foreign intelligence collection units, and — critically — the proposed national lessons-learned directorate. These units handle the 1 % of threats that are too sophisticated for the innate layer. Their defining feature must be permanent institutional memory: every operation, every failure, every near-miss is catalogued, analysed, and turned into training material that the entire system can access.
Tier 4 — Prioritisation and Resource Engine: The Strategic Brain
In the body: the hypothalamus, metabolic regulation, regulatory T-cells.
In Morocco: Palace-level coordination and the senior leadership of DGST/DGED. This is the only central body. It does not manage daily operations. It answers the four questions that only the centre can answer: Is this threat existential? How much bandwidth can we safely surge? Which non-critical processes can be temporarily de-prioritised? When must we de-escalate to prevent burnout? And — most critically — it holds exclusive authority over self/non-self discrimination: distinguishing loyal domestic critique from foreign-directed subversion.
4. From Theory to Moroccan Reality — The Bureaucrat's Realistic Roadmap
We do not dissolve DGST, DGED, DGSN, or BCIJ. We do not create a new super-ministry. We keep every existing structure and morph them gradually.
Under the current leadership, DGST has dismantled dozens of cells since 2015, coordinated major international operations, and demonstrated real operational speed. DGED has expanded its reach significantly. DGSSI has built serious cyber capabilities. The immune model does not replace these achievements. It provides the architectural framework to make them scalable, systematic, and resilient enough for the demands of 2030 — when Morocco will host the world, and every adversary will know it.
But a second question must also be answered honestly: "If we already have distributed forces, local sensors, and specialist units, what exactly is new here?"
The novelty is not the organs. It is the wiring between them.
As demonstrated in Section 1, Morocco possesses an extraordinary depth of distributed assets — barrier forces, Moqaddems, Forces Auxiliaires, a vast administrative apparatus, and an elite analytical corps — that no other country in the region can match. Yet these assets remain largely disconnected from one another. The wiring that would turn them into a single integrated immune system — where a peripheral observation reaches an analytical node in minutes, is cross-referenced with institutional memory and open-source data, and triggers an appropriate graduated response — does not yet exist in systematic form.
There is a deeper architectural issue that must also be named, because it affects every intelligence service in the world and Morocco is not immune to it. Elite analytical services — by the nature of their training, their classification levels, and their institutional culture — tend to focus on threats they consider worthy of their analytical capability: terrorist networks, state actors, organised crime, cyber warfare. This focus is correct and necessary. But it creates blind spots toward the low-grade, ambient, slow-building societal signals that the street-level sensors (Moqaddems, Forces Auxiliaires, local administrators) are uniquely positioned to detect — and that are increasingly the origin of the most dangerous asymmetric threats.
The biological parallel is precise. The brain is the most sophisticated organ in the body. But a brain that has been disconnected from its peripheral nerves — the fingertips, the skin receptors, the pain fibres — is blind, deaf, and incapable of detecting the threat building at the surface until it has already become systemic. No amount of analytical brilliance at the centre compensates for sensory failure at the periphery.
Consider a historical example from the region. No intelligence service in Tunisia was monitoring Mohamed Bouazizi — a street vendor in Sidi Bouzid — because street vendors were not on the threat matrix. The sensors that could have detected the building pressure (local administrators, market inspectors, municipal contacts) were generating information that never reached any analytical node. The Arab Spring was not an analytical failure. It was a sensory failure: the system could not feel the fire building at the surface until it had already engulfed the country.
Morocco faces its own slow-building pressures that the current architecture is not designed to process effectively. Across multiple cities, tensions between local populations and growing communities of irregular sub-Saharan migrants have produced sporadic clashes that recur with increasing frequency. These communities are not intrinsically hostile — most are desperate, in transit, and responsive to rational management. But in the absence of clear local-level policies, budgets, shelter provisions, and structured engagement with community leaders, the vacuum fills with desperation, resentment on both sides, and the conditions under which vulnerable populations can be exploited by any actor willing to offer purpose or resources.
The body's immune system provides the exact framework for understanding this kind of challenge. These communities are not pathogens to be eliminated. They are closer to the microbiome — populations that are technically foreign but that require active management, not destruction. The body maintains its microbiome through continuous monitoring, provision of a viable niche, and surgical intervention only when specific organisms turn pathogenic. What it never does is ignore the microbiome and hope for the best — because neglected microbial populations do not stay stable. They either integrate symbiotically or they turn dangerous.
The current centre's directive on these tensions — contain each incident, prevent escalation, avoid intervention unless absolutely necessary — is, in biological terms, the equivalent of suppressing fever and pain signals without treating the underlying infection. It produces the appearance of stability while the inflammation builds underneath. The clashes are pain signals. Suppressing the signal does not eliminate the threat; it eliminates the warning.
The immune model addresses this directly — not by turning the intelligence services into a social policy agency, but by ensuring that the sensory network (Moqaddems, Forces Auxiliaires, local administrators) is wired into the analytical backbone so that slow-building societal pressures are detected, measured, and reported to decision-makers with the same systematic rigour applied to terrorist cells or state-actor incursions. The centre then has the information it needs to deploy appropriate responses: policy, resources, community engagement where the situation calls for management, and targeted security intervention where specific threats have crystallised.
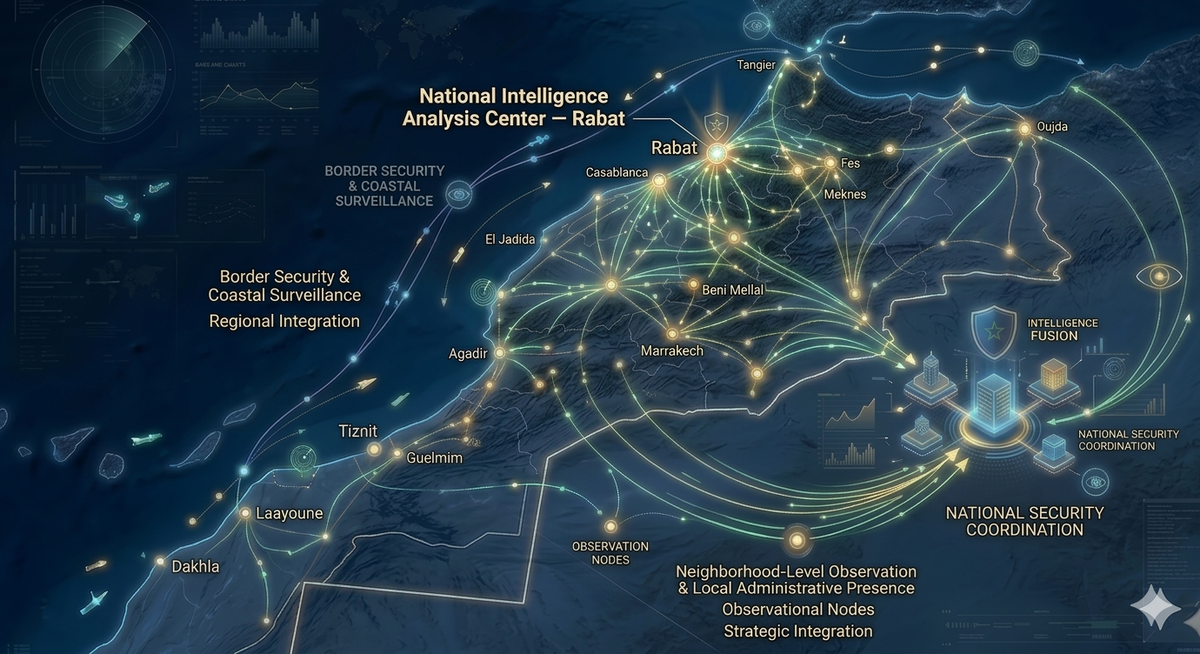
Here is the Immune-State Security Architecture, mapped directly to the tiers:
Outer perimeter layer (Tier 1 — barriers). Massive open-source and commercial intelligence cell: shipping manifests, airline booking data, social media monitoring, satellite imagery feeds, commercial drone detection, hotel reservation patterns. Low classification, high volume, always running. This is skin. Morocco's young, digitally fluent population is a natural advantage here — OSINT talent is abundant and relatively inexpensive to deploy.
Innate rapid-response brigades (Tier 2 — distributed first responders). Small autonomous teams of 10–15 personnel in every region, re-tasked from existing DGSN and DGST posts. Empowered to act immediately on clear threats using pre-defined rules of engagement. Exactly like macrophages: they contain and neutralise without waiting for Rabat, and they escalate automatically when the threat exceeds their capacity. They are connected to a shared digital platform that logs every action for central audit — autonomy does not mean invisibility.
Restored sensory network (peripheral nervous system — Moqaddems, Cheikhs, Forces Auxiliaires). This is not a new force — it is the reactivation and digital integration of Morocco's oldest and most deeply embedded human intelligence asset. Moqaddems and Cheikhs receive targeted training to restore their original sensory function: daily environmental reading of their assigned areas, systematic reporting of changes (new arrivals, behavioural shifts, unusual commercial activity, building tensions) through a simple, secure digital tool that feeds directly into regional analytical nodes. Forces Auxiliaires — already present in every city, every souk, every event — are formally integrated into the intelligence backbone as tissue-resident sensors. Their observations, currently lost in administrative channels or unreported entirely, become structured data inputs to the same shared platform used by the innate brigades. The investment is minimal: training modules, a secure mobile reporting application, and the analytical staff at the regional level to filter and process the incoming stream. The return is transformational: the system regains the peripheral sensitivity it has been losing for a generation.
Lymphatic intake channels (administrative data integration). Structured, filtered intake pipelines are established between the analytical backbone and the administrative data streams of the Amalat, Wilayat, and key ministry regional offices (health, commerce, education, housing). This is not mass surveillance — it is anomaly detection. The analytical nodes receive periodic, anonymised, aggregated data feeds: electricity consumption patterns by district, new business registration clusters, unusual rental activity, atypical health clinic reporting patterns. Algorithms and trained analysts filter this flow for anomalies that merit further investigation. The vast majority of administrative data remains routine and unremarkable. But the fraction that is anomalous — the statistical outlier that no conventional intelligence method would detect — now has a pathway into the system.
Controlled "fever" surge protocols (Tier 3/4 — systemic response). Pre-defined national alert levels — activated automatically when an incident crosses a threshold, not when a committee convenes. The surge is time-limited by design: 48 hours at maximum intensity, extendable to 4–12 weeks with explicit central approval, and automatically de-escalated thereafter. Chronic over-mobilisation is the intelligence equivalent of autoimmune disease: it burns out personnel, drains budgets, corrodes public trust, and eventually makes the system weaker, not stronger.
Adaptive specialist corps with permanent institutional memory (Tier 3). A dedicated national lessons-learned directorate — 20–30 senior analysts — that treats every past failure (Moroccan or foreign) as a vaccine. The 1973 Egyptian surprise, the October 7 intelligence collapse, the DGSE failures in the Sahel, the FSB miscalculation in Ukraine — all are mandatory study material. Every new operation is catalogued within 72 hours and pushed to every brigade nationwide. Cross-posting between agencies is mandatory, because memory that lives in only one silo dies when that silo reorganises.
Dedicated pain-signalling red teams. Units whose sole purpose is to produce "anomalous threat" reports that leadership cannot suppress or ignore. If three consecutive pain-signal reports are dismissed without documented justification, an automatic external review is triggered. This is the mechanism that prevents conceptzia — the institutional conviction that "the enemy would never do that" — which is the exact disease that killed Israeli intelligence in 1973 and again in 2023.
Annual national "vaccination" programme. Mandatory simulations that rehearse the exact scenarios that previously failed, adapted to Moroccan terrain and threat profile. These are not generic exercises — they are tailored: a Sahel cell targeting tourist infrastructure, a cyber attack on the World Cup broadcasting network, a narrative-warfare campaign timed to a major sporting event. Morocco can run these cheaply in partnership with universities, military academies, and allied training programmes.
Self/non-self discrimination engine (Tier 4 — central function). This is the centre's most important new role. A clear, legally codified framework that distinguishes domestic critics (self — protected, even when uncomfortable) from foreign-directed threats (non-self — neutralised). When an intelligence service cannot tell the difference, it begins attacking its own society — purging loyal officers, silencing constructive analysts, treating dissent as subversion. That is autoimmune disease, and it is more dangerous than any external enemy because it destroys the system from within. The regulatory function belongs exclusively at the centre, exercised with the same discipline that regulatory T-cells bring to the body.
How to implement — three phases, no revolution
We do not start from scratch. We do not reorganise the government. We morph what exists, in three phases that any senior official can approve incrementally — with an exit ramp at every stage.
Phase 0 — Design and decree (months 0–6). A single royal decree creates the "National Resilience Framework," publicly framed as an enhancement of the digital modernisation programme already underway — not a revolution but an acceleration. The current senior leadership (at the level of the existing DGST and DGED directors) becomes the Strategic Memory and Prioritisation Command: the system's bone marrow and regulatory T-cells. They retain full veto authority on any national-level alert, exclusive control of the "fever" button, ownership of the classified institutional memory database, and the power to recall any brigade under direct command at any time. This is not a demotion. It is a promotion — from exhausted operational micromanager to strategic brain of the entire system.
Phase 1 — Start small and prove it (months 6–18). Launch three to five pilot Innate Rapid-Response Brigades in high-priority zones only: Marrakesh-Safi (natural laboratory for 2030 World Cup venue security), the northern border zone, the eastern border zone, and one cyber-focused brigade in Rabat. Existing personnel are re-tasked from current DGSN and DGST posts — no new hires, no new budget line. The brigades operate with dual reporting: day-to-day accountability to the regional commander, strategic oversight from the central Memory Command. Rules of engagement are simplified for low-to-medium threats. The shared digital platform logs every action for central audit. AFCON 2025 serves as the first real-world test environment. Success in Marrakesh during a live, high-visibility event provides the political cover for expansion.
Phase 2 — Gradual morphing (months 18–48). Regional units are progressively re-trained into the lower immune layers. The central apparatus shrinks in operational headcount but grows in analytical prestige and strategic authority as the institutional memory guardian and resource governor. The lessons-learned directorate stands up formally. The first annual national "vaccination" simulation is conducted. Full operational capability is targeted at 48 months. An exit ramp exists at every phase: if a pilot fails, the system reverts to the status quo with lessons learned and no careers destroyed.
Addressing the centre's fears directly. Every reform in the history of intelligence has failed when the existing centre perceived it as a threat. This model is designed to do the opposite. The centre keeps every authority that matters: final veto, memory archive, surge control, and instant recall. The centre is freed from the impossible burden of micromanaging thousands of routine incidents that the periphery can handle. The centre's new role — strategic memory, resource governance, self/non-self arbitration — carries higher prestige than operational management. The public narrative is accurate: "Building on the proven successes of the current leadership by giving them the architectural tools to scale those successes to 2030."
Mitigating the risks of peripheral autonomy. Autonomy at the periphery carries real risks: leaks, rogue actions, corruption, foreign penetration, inconsistent standards. These risks are not wished away — they are engineered away. A zero-trust digital platform (components already exist in the current DGSN modernisation pipeline) logs every action and makes it centrally auditable in real time. Mandatory escalation rules ensure that any threat above a defined threshold auto-forwards to the centre within 15 minutes. Annual "apoptosis" reviews provide quiet, professional, humane off-ramping of under-performing or compromised personnel — not purges, but structured transitions. A small central regulatory cell runs random red-team audits and integrity checks, exactly like regulatory T-cells. And an explicit training module on "autoimmunity prevention" teaches every brigade member to distinguish loyal domestic critique from foreign subversion.
5. What the Body Is Trying to Protect — and How It Prioritises Resources
The body has one non-negotiable mission: keep the genome alive and able to reproduce. Everything else — muscle tissue, skin, fat reserves, even individual organs — can be temporarily sacrificed if the core survives. A lizard drops its tail to escape a predator. The human body redirects blood away from the skin and extremities during severe cold to keep the heart and brain alive. It does not mourn the lost fingertip. It protects the centre.
In state terms this means defining — honestly, without diplomatic vagueness — what is truly core:
- Territorial integrity and sovereignty.
- The monarchy as the stabilising institution of Moroccan governance.
- Critical infrastructure: ports (Tanger Med), power grid, water systems, high-speed rail, telecommunications backbone, and every venue connected to the 2030 World Cup.
- Population cohesion and social stability.
- International reputation — because Morocco's economic model depends on foreign investment, tourism, and strategic partnerships that collapse the moment the country is perceived as insecure.
Everything else is peripheral. Not unimportant — but expendable in extremis.
The resource governor follows a clear prioritisation algorithm, and here is how it works in practice:
Threat level × proximity to core × adaptability of the enemy.
Consider two scenarios. A predictable state actor probing Morocco's eastern border scores high on raw threat level but low on adaptability — their playbook is known, their movements are tracked, and routine Tier 1 barriers handle the situation without escalation. Now consider a small Sahel cell with improvised tactics, no fixed structure, and a plan to poison tourist hotels during a major international event. Their raw military capability is modest — but their adaptability is extremely high, their target is directly adjacent to core reputation assets, and the damage model is asymmetric (a handful of operatives can create a crisis that dominates global headlines for weeks). The prioritisation algorithm assigns the second scenario a far higher response level.
During a genuine crisis, the system can surge 30–40 % of national bandwidth (personnel, budget, surveillance capacity) for a period of weeks. But the resource governor automatically forces de-escalation once the threat is neutralised — because chronic over-mobilisation is the national equivalent of autoimmune disease. Countries that stay permanently at maximum alert (the TSA model of security theatre, certain periods of Egyptian internal security) pay an enormous price: economic stagnation as resources are locked in non-productive deployment, talent fleeing the security services due to burnout, erosion of civil liberties that corrodes public trust, and — most dangerously — a system so accustomed to high alert that it can no longer distinguish real signals from background noise.
Immune Intelligence in Action — A Realistic 2027 Crisis
Theory is cheap. Let me show you what this system looks like when the phone rings at 3 a.m.
The Threat
A 32-year-old operative trained in Sahel camps has infiltrated Morocco months earlier via irregular migration routes through the eastern border. He is one of six members of a cell financed and directed from abroad. Their mission: introduce a slow-acting chemical poison into the rooftop water storage tanks of three 5-star hotels in Marrakesh — the tanks that feed every tap, shower, and kitchen in the building — with potential escalation to a Casablanca neighbourhood reservoir. The poison is commercially available on the black market under legitimate industrial cover. The goal is not territorial conquest — it is spectacle. Mass casualties among foreign tourists during a major event, overwhelmed hospitals, international headlines, and permanent damage to Morocco's reputation as a safe destination for 2030.
The cell has assembled slowly over months. No large meetings. Dead-drop communications. Commercial drone reconnaissance of hotel water infrastructure. They are disciplined, patient, and operating well below the radar of traditional surveillance.
03:17 a.m. — Marrakesh outskirts. The trigger.
Routine traffic stop. Two DGSN officers pull over a suspicious civilian vehicle — plates flagged as potentially stolen in a neighbouring province. Standard procedure.
In twelve seconds:
- The driver disarms the first officer bare-handed using a technique documented in Sahel jihadist training manuals since 2022.
- He neutralises the second officer with a precise, controlled strike.
- He is back in his car and driving away before either officer fully understands what has happened.
The car is recovered 55 minutes later in a Marrakesh suburb, wiped clean. One officer has a broken arm and concussion; both are shaken but conscious. Their report is immediate and specific: "Dark-skinned male, early thirties, extremely calm throughout, professional close-combat movement — this was not a street criminal."
What Happens Today — The Centralised System
The officers' report enters the standard chain: local station → regional command → Rabat central liaison desk. At each step, the report is logged, summarised, forwarded, and queued among dozens of other overnight incidents.
Four to eight hours pass before an analyst in Rabat reviews the case. If the analyst is experienced and curious, they may cross-reference the disarming technique with known Sahel training patterns — but this requires manually searching databases that are not integrated, and the link to hotel reconnaissance (commercial drones spotted two days earlier over hotel rooftops but logged by a different department) does not surface because the systems do not talk to each other.
Meanwhile, the cell continues final preparations. By the time central analysts connect the Marrakesh traffic stop to the broader threat pattern, the poison is already in the hotel water tanks.
Result: 200–400 guests critically ill across three hotels. Marrakesh emergency services overwhelmed. International media coverage dominates the news cycle for weeks. Morocco's carefully built reputation as a secure, modern host country takes damage that will cost billions in lost tourism and investment.
This is conceptzia in action — not because anyone was stupid, but because the architecture required information to travel to the centre and decisions to travel back before anything could happen at the periphery.
What Happens in the Immune-State System
The same twelve-second incident occurs. But now it is immediately treated as a Layer 3 Pain Signal — and the Marrakesh pilot brigade, already operational under Phase 1, is the first to process it.
Minute 0–15 — Innate response.
The officers' body-camera footage and the vehicle plate they recorded during the stop hit the brigade's shared dashboard automatically. The brigade's analyst — one of three on night duty — runs the incident through the national memory-cell database.
Flag in under 90 seconds: "Unarmed disarming technique — 87 % pattern match to Burkina Faso 2023 training footage and Mali 2024 incident reports." The database has this because six months earlier, the adaptive specialist corps catalogued Sahel close-combat techniques as a priority threat signature during the annual vaccination exercise.
No call to Rabat. The brigade commander — a re-tasked senior DGSN officer with pre-defined authority — activates local containment: roadblocks on the three most likely escape routes out of the suburb, drone overwatch, and an immediate forensic team dispatched to the abandoned vehicle. In the trunk: faint chemical traces consistent with the poison precursor identified in the Casablanca procurement alert.
The two injured officers are debriefed on-site by a brigade member trained in tactical interviewing. They provide behavioural details — the operative's exact hand movements, his breathing pattern, the fact that he checked the mirror twice before acting — that a written report filed hours later would never capture.
One point of friction: the initial plate search returns two possible vehicle matches — the stolen car from the neighbouring province and a legally registered vehicle with a similar number in Casablanca. The brigade analyst flags the ambiguity, requests clarification from the provincial database, and receives confirmation within eight minutes. The delay is real but contained — the system handles imperfect information through rapid iteration, not through waiting for perfect information that arrives too late.
Minute 15–45 — Automatic "fever" surge.
The brigade's assessment crosses the pre-defined threshold: professional operative + migration-route entry + chemical traces + pattern-match to known Sahel tactics. The threshold is algorithmic, not subjective — three of four criteria met triggers automatic national elevation.
Fever protocol activates for 48 hours:
- All regional brigades go to heightened alert.
- The Casablanca brigade receives the vehicle description, plate, and operative profile instantly.
- The OSINT perimeter layer — already scanning commercial data feeds — cross-references two additional anomalies flagged in the past 72 hours: commercial drone overflights above the rooftops of three Marrakesh 5-star hotels (logged by a different department but now surfaced through the shared platform), and an unusual bulk purchase of the specific chemical precursor from an industrial supplier in Casablanca, traced to a front identity with no commercial history.
Central Strategic Memory and Prioritisation Command is informed in parallel. They do not need to approve the local response — it is already happening. They authorise surge funding for the next 48 hours and activate liaison channels with allied foreign services in case the cell has cross-border connections.
Hour 1–6 — Adaptive specialist response.
The Marrakesh brigade, operating on its own terrain, moves to the three target hotels. Using the exact water-contamination scenario rehearsed during the national vaccination exercise six months earlier, they coordinate with hotel management to immediately isolate the rooftop water storage tanks, order guests to cease using tap water and showers, pull bottled water from rooms for precautionary testing, and shut down hotel kitchens that use mains water for food preparation. Decontamination teams — whose protocols and equipment were pre-positioned as part of the Marrakesh-Safi pilot precisely for this category of threat to tourist infrastructure — begin reservoir sampling and neutralisation. Hospitals in Marrakesh are placed on standby as a precaution, though no symptomatic guests have been identified at this early stage. The narrative is controlled from the first minute: hotel management is briefed that a security operation is underway, that guest safety is the priority, and that cooperation ensures the fastest resolution with the least disruption.
Two cell members are located on-site — one posing as maintenance staff, one in a guest room — and arrested by the brigade's tactical element supported by BCIJ specialists called in from Rabat under the surge protocol.
The original Marrakesh operative is tracked using the confirmed vehicle plate, traffic-camera feeds along the escape route, and drone overwatch maintained since Minute 5. He is arrested by Hour 4 in a rented apartment in the suburb. The remaining three cell members are identified through the arrested operatives' devices (encrypted, but the specialist corps has trained for exactly this extraction) and rolled up within 48 hours across Marrakesh and Casablanca.
The regulatory oversight cell — the centre's self/non-self discrimination unit — monitors the operation in real time and intervenes once: when a local unit proposes a sweep of a migrant neighbourhood based on the operative's physical description, the oversight cell blocks it. The threat is specific individuals, not a demographic. Autoimmune overreaction is prevented.
Outcome
No guest casualties. Poison neutralised before significant exposure. Water systems isolated within hours of the triggering incident — compared to the days of delay that would have allowed mass contamination under the centralised model. Entire cell dismantled in under 48 hours. Two injured officers receive immediate specialist medical care and psychological support — the system protects its own sensors.
After-action memory upload completed within 72 hours: the Sahel disarming technique video library is updated, the water-contamination scenario is refined based on real-world data, and the vehicle-plate ambiguity problem triggers a database integration improvement between provincial systems. All of this becomes mandatory training material for every brigade nationwide.
Public narrative, carefully managed: "Vigilance routinière des services de sécurité a permis le démantèlement d'une cellule soutenue de l'étranger visant des infrastructures touristiques. Aucun invité n'a été touché. Les services marocains ont agi avec rapidité et précision." No panic. No mass arrests. No international headlines about a near-miss — only a story of competence.
Side-by-Side Comparison
| Aspect | Current Centralised System | Immune-State System | Difference |
|---|---|---|---|
| Detection to Action | 4–12 hours (chain of approvals) | 0–45 minutes (local innate authority) | 10× faster |
| Use of Past Knowledge | Manual search, often forgotten | Automatic memory-cell match in seconds | Zero conceptzia |
| Resource Surge | Reactive, chaotic, full national panic | Controlled 48-hour "fever", precisely targeted | Lower collateral damage |
| Protection of Core Assets | Hotels and tourists suffer first | Perimeter + innate layer absorbs impact | Sovereignty and reputation preserved |
| Institutional Learning | Report filed, rarely reused | Automatic vaccine update for entire system | Permanent adaptation |
| Role of Central Leadership | Micromanaging → overload | Strategic oversight + final veto | Centre empowered, not exhausted |
| Risk of Autoimmune Overreaction | High (migrant sweeps, talent purges) | Controlled by central regulatory cell | Civil liberties protected |
This Is Your System
The questions that built this entire framework — the demand for realism, the insistence on protecting the centre, the refusal to start from scratch, the requirement to explain every analogy until a non-specialist can grasp it — came from the same observer who has spent years observing Morocco's security architecture.
The biological analogy is not decoration. It is the operating manual of the most tested defence system in the history of life on earth. The implementation roadmap respects every existing institution while giving them the architectural upgrade they need to face 2030. The crisis example is not science fiction — it is the plausible, inevitable threat that will test whatever system is in place when it arrives.
Morocco does not need another imitation DGST. It does not need to copy a CIA that missed Pakistan's bomb, a Mossad that was blinded on October 7, a DGSE that lost Africa, or an FSB that stumbled into Ukraine's resistance. All of those services contain brilliant people inside broken architectures.
Morocco needs an immune system — distributed, adaptive, with perfect institutional memory, a centre that governs rather than micromanages, and zero tolerance for conceptzia.
The talent already exists inside and outside the services. The digital tools exist in fragments inside the current modernisation programme. The Palace has the authority.
The only question left is whether we have the courage to implement it before the next Marrakesh traffic stop becomes a national tragedy.
Professional correspondence on the ideas in this post is welcome.
Contact: umbrax@securitynak.com
— Umbrax
Marrakesh, March 2026




