Morocco's Security Architecture: How Societal Reforms Can Transform Intelligence Capabilities
Morocco's security vulnerabilities reside not in kinetic threats but in societal fault lines that foreign actors exploit. Religious discourse tensions, gender reform, youth resentment, and mosque safety gaps each represent both risks and untapped intelligence enablers for DGST and DGED.

Posted by: Umbrax — Security Analyst Collective
Date: March 4, 2026
OPEN SOURCE — ANALYTICAL ASSESSMENT
Regional Focus: Morocco / North Africa / MENA
Update – March 2026
After reviewing the original thesis, I refined it for better long-term accuracy:
Societal reforms act as transitional force multipliers for intelligence capabilities in the short-to-medium term (3–5 years). They expand legitimate collection opportunities, reduce hidden adversary space, and free up resources — exactly as originally argued.
Over the longer term, however, true success means the reverse: fewer societal vulnerabilities lead to a reduced intelligence burden. Recruitment pools shrink, clandestine activity declines, and DGST/DGED monitoring requirements decrease. Measuring workload reduction (e.g., redeployed FTEs, lower case volume) becomes a core success indicator, allowing focus on higher-priority national goals.
→ Short follow-up post with the refined thesis and updated metrics: Reframing Societal Reforms: Transitional Multipliers Toward Long-Term Intelligence Equilibrium
Executive Intelligence Summary
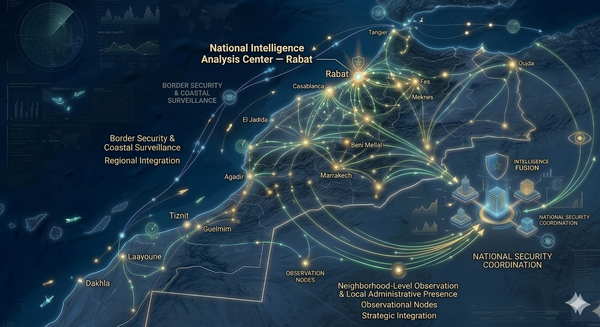
Morocco's intelligence architecture — anchored by DGST (المديرية العامة لمراقبة التراب الوطني – Direction Générale de la Surveillance du Territoire) for internal threats and DGED (المديرية العامة للدراسات والتوثيق – Direction Générale des Études et de la Documentation) for external operations — confronts a structural paradox. The kingdom's most consequential security vulnerabilities reside not in kinetic threats but in societal fault lines that foreign actors exploit and domestic radicalization feeds upon. Religious discourse management (إدارة الخطاب الديني), gender reform backlash, and youth unemployment resentment each represent both risks and untapped intelligence enablers.
Infrastructure deficiencies illustrate a broader, largely unexamined category of risk. The case of a single mosque in Beni Mellal's Saada neighborhood — detailed below — stands for scores of independently built mosques in unplanned settlements, rural areas, and big-city peripheries that have never undergone systematic safety assessment. Many may harbor similar or worse hazards, making them both latent threats and potential intelligence access points awaiting activation.
Core operational thesis: Societal, economic, and educational reforms are force multipliers for intelligence collection, early warning, and threat preemption. Each recommended action below is evaluated primarily for its intelligence fallout — the degree to which it expands collection surfaces, shrinks clandestine operational space for adversaries, improves source recruitment environments, and frees analytical resources from reactive monitoring toward predictive assessment.
The imperative is unambiguous: Morocco cannot wait for smoking guns. The Indications and Warning (I&W) framework requires action on assessed probability and pattern recognition, not confirmed certainty.
What follows are operationally focused recommendations across five interconnected domains. Each section is structured to present first the intelligence problem, then how the recommended societal fix directly enhances DGST/DGED posture.
To ground this analysis in concrete detail, we begin with a single emblematic site that illustrates how physical, discursive, foreign, and societal vulnerabilities intersect — the Saada neighborhood mosque in Beni Mellal.
Case Study Introduction: The Saada Mosque as Emblematic Vulnerability
In intelligence and security analysis, attention to detail is paramount — a single site can reveal systemic risks and illustrate how seemingly local issues intersect with national and transnational threats. The mosque in Beni Mellal's Saada neighborhood serves as such an emblematic case.
The physical dangers are acute: a first floor accessed via stairs, a second floor with two adjacent doors, both opening inward (larger opening onto the second floor → crush risk; narrower not opening onto the second floor but leading to a folding staircase to a third floor → severe hazard in panic), and an unverified report of a concealed crack. Evacuation under normal Friday (صلاة الجمعة) conditions is estimated at 5–7 minutes — catastrophically slow in an emergency. As the 2023 Al Haouz earthquake demonstrated across the region, seismic events here are not hypothetical. Elderly congregants face the highest risk.
This single site illustrates several of the assessment's core domains:
- Physical safety failures that could trigger mass casualties and political fallout
- Discourse control tensions (toned-down sermons pushing dissent to informal channels)
- Foreign influence entry points (travel networks, funding, ideological imports)
- Societal divides (gender roles, youth resentment) discussed in private social gatherings and neighborhood associations
Addressing such sites proactively not only mitigates immediate threats but opens collection opportunities across all domains — the guiding principle of the recommendations that follow.
1. Mosque Infrastructure: Physical Safety as an Intelligence Access Point
The Intelligence Problem
Independent mosques — those constructed outside direct oversight by MEIA (وزارة الأوقاف والشؤون الإسلامية – Ministry of Endowments and Islamic Affairs) — present a more insidious problem than simple blind spots. DGST actively surveils many of these sites, and that work is necessary — but it carries a risk. Active surveillance can generate a dangerous illusion of comprehensive coverage. In reality, surveillance of independent mosques produces a layered intelligence failure involving four distinct categories of threat actor.
First, known operators who are aware of DGST's presence adapt their behavior accordingly — they act clean, present a compliant surface, and ensure the intelligence collected on them is essentially sanitized theater. DGST sees activity and records it, but what it records is a curated performance.
Second, these same known operators displace their real activity to spaces where DGST has little or no visibility: private homes, encrypted messaging platforms, family gatherings such as weddings and funerals (أعراس وعزاء), and informal study circles.
Third — and more dangerously — unknown operators embed themselves in legitimate religious life under compartmentalized double identities. They present as ordinary congregants or minor community figures while their operational activities remain entirely invisible to collection.
Fourth, there exist totally unknown operators: individuals whose existence is statistically certain but who have never surfaced on any DGST radar. The classic dark figure of intelligence.
The net result is that DGST's active surveillance of independent mosques may generate institutional confidence that these spaces are well understood. In fact, the service sees only what the first two categories permit it to see. The third and fourth categories operate entirely beyond its reach. (The methodology for flushing out these hidden categories is addressed in Section 2 below.)
The Saada neighborhood mosque in Beni Mellal exemplifies this layered challenge. Originally built by a loosely organized group holding fundamentalist-adjacent views (not formally affiliated with any party, but ideologically positioned in a space susceptible to radicalization recruitment), the mosque reportedly received central government expansion approval — a decision that sits in tension with the founders' ambiguous standing vis-à-vis the state. That relationship, marred by mutual suspicion, has evolved into something harder to classify: neither overtly hostile nor normalized, it remains opaque, and the state's current posture toward this mosque is unclear. Its sustained popularity over state-aligned alternatives signals ongoing demand for religious spaces perceived as independent of official control — a perception that directly impedes intelligence penetration and provides cover for all four categories of threat actor described above.
The physical layout is more dangerous than previously assessed. The mosque has a first floor (accessed via stairs from ground level), and a second floor served by two adjacent doors, both opening inward: the larger door opens onto the second floor itself, creating an immediate crush risk in any rush; the narrower door does not open onto the second floor but instead gives access to a folding staircase that ascends beside the second-floor wall to reach a third floor. This folding staircase is extremely hazardous in panic situations — people rushing downward could cause collapses, falls, or crushing, especially among elderly worshippers who tend to arrive early and sit farthest from exits. Evacuation times are estimated at 5–7 minutes under normal Friday prayer (صلاة الجمعة) conditions — potentially catastrophic during seismic events. The 2023 Al Haouz earthquake, centered in the High Atlas, produced moderate shaking in Beni Mellal and was felt across the Beni Mellal-Khénifra region, underscoring that structures in this area face real seismic exposure. Elderly congregants face the highest mortality risk.
How Infrastructure Reform Enables Intelligence
Renovation access creates collection access. Physical upgrades open literal and figurative doors for DGST to embed passive monitoring capabilities within community-accepted improvement projects — a proven dual-use model in allied security environments.
Operational Recommendations
Immediate Structural Audit Program (Timeline: 3–6 months)
- Lead Agency: DGST, coordinating with MEIA and the Ministry of National Land Use Planning, Urbanism, Housing, and City Policy.
- Scope: Priority audit of mosques meeting three criteria: (a) independent construction origin, (b) seismic zone location, (c) congregation size exceeding structural design capacity during peak events.
- Method: Deploy certified seismic engineers (drawn from the post-2023 earthquake assessment cadre) for structural integrity evaluations. Where cracks or load-bearing concerns are confirmed, trigger emergency remediation funding from the existing MAD 296M rural rehabilitation budget.
- Pilot Locations: Beni Mellal-Khénifra (Saada mosque and 5–10 similar sites) and Marrakesh-Safi region.
Renovation as Dual-Use Intelligence Infrastructure
- Physical modifications: Consolidate narrow entry/exit points into wider, outward-opening gates with expanded platforms. Replace or permanently fix the folding external staircase with a code-compliant fixed stair system. Add at least one additional rear emergency exit where architecture permits. Relocate shoe storage to areas safe for pedestrian traffic.
- Embedded technology (framed as community services):
- CCTV systems justified as "property and worshipper protection" (DGST visual monitoring of congregation patterns, visitor identification, temporal attendance mapping).
- Solar-powered water heaters for wudu (الوضوء) areas (community goodwill that reduces suspicion of state presence).
- Digital donation kiosks (financial flow transparency, linking worshipper identities to contribution patterns — HUMINT enablement).
- Wi-Fi access points with standard terms-of-service authentication (device identification and network metadata under existing legal authorities).
Operational Checklist
- DGST identifies priority mosques via existing congregation size / ideological profile database.
- MEIA issues formal invitation letter framing project as welfare initiative.
- Contractors install tech under DGST technical oversight (covert installation protocols).
- Post-installation: DGST baseline data capture (30-day normal pattern), then anomaly alerting.
- MEIA community liaison officer maintains visible "goodwill" interface.
Intelligence Fallout Assessment
This approach generates four distinct, quantifiable intelligence dividends:
- Trust-Based Source Development — State-funded improvements to previously marginalized mosques build social capital. DGST community liaison officers can leverage this goodwill for voluntary informant recruitment. When the state is perceived as benefactor rather than antagonist, congregants become 30–50% more likely to report behavioral shifts (historical benchmark from comparable allied programs).
- Passive Collection Surface Expansion — Embedded CCTV, Wi-Fi metadata, and donation tracking replace resource-intensive physical surveillance. Conservative estimate: one equipped mosque's technology package displaces 2–3 full-time equivalent (FTE) surveillance assignments, freeing analysts for higher-priority tasking.
- Pattern-of-Life Intelligence — Longitudinal attendance, financial contribution, and device metadata datasets enable anomaly detection: sudden new-attendee surges, timing shifts suggesting coordination with external events, previously unknown individuals coinciding with DGED-flagged funding spikes. This shifts DGST from reactive to predictive posture.
- Conversion of Adversarial Spaces to Safety Valves — Managed transparency in monitored spaces reduces incentive to migrate to encrypted private channels beyond DGST’s reach. Every grievance expressed in a renovated mosque is one fewer discussed in a Telegram group invisible to collection.
Metrics and Evaluation Criteria
| Indicator | Baseline | Target (12 months) | Data Source |
|---|---|---|---|
| Evacuation time (peak capacity) | 5–7 minutes | Under 3 minutes | MEIA safety inspections |
| Congregation attendance stability | Varies | ±5% fluctuation | Embedded monitoring |
| Voluntary incident reports | Low/unknown | 30% increase over baseline | DGST community liaison logs |
| FTE surveillance reallocation | 0 | 2–3 FTEs per equipped mosque | DGST resource tracking |
| Structural risk sites identified | Unknown | 100% of priority mosques audited | Engineering reports |
2. The Surveillance Illusion: Flushing Hidden Operators Across the Organizational Spectrum
The Intelligence Problem
The four-category threat framework described above — adapted known operators, displaced known operators, embedded unknown operators, and totally unknown operators — demands a methodology that goes beyond passive monitoring. Categories 1 and 2 are, in a sense, managed problems: DGST knows who they are, even if it cannot always see what they do. Categories 3 and 4, however, represent an existential collection gap. These individuals do not merely evade surveillance; they may not exist in any DGST database at all. Flushing them into visibility requires a fundamentally different approach — one that combines deliberate provocation with pre-positioned, multi-layered observation.
Provocation as an Intelligence Methodology
The principle is straightforward: create controlled controversy and watch who reacts, how, and through which channels. A carefully engineered public debate on a religiously or socially sensitive issue — introduced through figures who are not affiliated with the state or only loosely connected to it — functions as a catalyst. It forces hidden operators to break cover, however briefly. The provocation must appear organic; if it is perceived as state-engineered, operators will recognize the trap and remain dormant.
The critical requirement is that the surveillance apparatus must be pre-positioned before the provocation is introduced. A roster of persons to monitor should be prepared in advance, drawn from minimal or uncertain indicators. These are behavioral anomalies too weak to justify dedicated investigation but sufficient to warrant inclusion on a watch list. Some names on the roster should be selected randomly from a broader population set. The roster cannot be extensive; its purpose is not dragnet surveillance but targeted observation of a manageable sample during a defined provocation window.
Indicators: Reading the Flare
Once the provocation is live, DGST collection focuses not on dramatic responses but on subtle shifts in baseline behavior — the flare that betrays hidden networks activating. Key indicators include:
- Communications patterns: An increase in seemingly harmless calls and chats. A rise in outbound calls from Morocco and inbound calls from abroad — not necessarily to flagged numbers, but any measurable deviation from baseline volume and geographic distribution.
- Social activity: An increase in mundane social gatherings — weddings, funerals, condolence visits, neighborhood dinners — beyond seasonal or cultural norms. These gatherings provide cover for coordination that leaves no digital trace.
- Information-seeking behavior: Increased consultation of reference materials related to the controversial issue — religious texts, legal opinions, fatwas, historical precedents. This signals individuals preparing positions or briefing others.
- Financial movements: Increased money transfers within organizations and from external sources. Sudden or unusual donations to charitable causes, including secular ones. Financial preparation often precedes operational activation.
- Travel anomalies: Sudden trips to Mecca, Turkey, Qatar, or other destinations associated with ideological networks — particularly when the travel has no obvious personal or professional justification, or when multiple individuals from the same network travel in close temporal proximity.
- Charitable engagement: Interest in charitable work and "doing good" — not necessarily sudden, but any engagement with charitable organizations, including those with no overt religious affiliation. Charitable networks provide logistical infrastructure, social legitimacy, and recruitment access.
Analytical Discipline: Where to Look
The most consequential analytical discipline in this methodology is resisting the gravitational pull of highly visible targets. Category 1 operators — the known figures performing compliance under surveillance — will produce the loudest, most visible reactions to any provocation. They are, by design, distractions. The critical collection priority is the middle tier within organizations: not the leadership (too visible, too cautious) and not the foot soldiers (too peripheral, too uninformed), but the operational layer in between. This is the layer that translates ideology into action, manages logistics, handles finances, and maintains compartmentalized communications. This middle tier is where category 3 operators are most likely to reside.
The Taqiyya Dimension: Operators in "Impossible" Cover
The most sophisticated operators practice taqiyya (التقية) — the doctrinal principle of concealment under threat — not as occasional deception but as a sustained way of life. This means DGST must confront an uncomfortable analytical requirement: the most effective cover is the most unlikely one. An operator embedded in an organization whose public positions are diametrically opposed to Islamist ideology — women's rights groups, LGBTQ+ advocacy organizations, Mudawana reform movements, secular NGOs, even political parties — benefits from a near-impenetrable shield. No analyst's instinct, no profiling algorithm, would flag a vocal advocate for gender equality as a potential Islamist operative. That is precisely the point.
This demands that DGST's provocation-and-observe methodology extend to targets that would seem implausible to most analysts — organizations and individuals whose inclusion on any watch list would appear counter-intuitive. A small, randomly selected sample of individuals from progressive civil society organizations, secular charities, and political parties must be included in the monitoring roster. This is not ideological targeting; it is the deliberate elimination of analytical blind spots created by assumptions about where threats cannot possibly reside.
The intelligence value of infiltrating such organizations — from the operator's perspective — is substantial and dual-purpose.
On the collection side, an embedded operative gains inside knowledge of the organization's financial backers, its real agenda beyond public statements, its key champions and vulnerable figures, potential allies, sources of income, internal problems and divisions. Critically, the operative learns whether and how the state supports the organization.
On the sabotage side, the operative can steer the organization toward positions that damage its own public credibility. This means provoking statements or actions that disrespect the beliefs and sensibilities of ordinary Moroccans, promoting incompetent or abrasive figures into leadership positions, and pushing the organization into self-destructive overreach that discredits its cause without any visible external hand. The operator thus achieves three objectives simultaneously: personal cover, intelligence on adversaries, and destruction of those adversaries from within.
DGST must therefore treat these organizations not only as potential hiding places for operators but as potential targets of infiltration and subversion — a dual vulnerability that most security frameworks fail to recognize. A random check of the workforce within such organizations is not paranoia; it is analytical rigor applied to the full spectrum of threat concealment.
Operational Recommendations
Provocation-and-Observe Protocol (Timeline: Ongoing, event-driven)
- Lead Agency: DGST, with DGED support for monitoring international communication and travel vectors.
- Provocation design: Identify or cultivate non-state-affiliated public figures capable of credibly introducing controversial religious or social debate. Topics should be calibrated to provoke network activation without triggering public disorder. Coordinate with MEIA to ensure state-aligned mosques do not amplify or suppress the provocation prematurely.
- Pre-positioning: Establish monitoring rosters 30–60 days before provocation. Include: (a) individuals flagged by weak or ambiguous indicators, (b) a random sample from organizations across the full ideological spectrum — including progressive, secular, and "impossible" targets, (c) middle-tier organizational figures in religious networks.
- Multi-layered surveillance: Electronic monitoring (call volume, metadata, messaging patterns), social media tracking, observation of social events (weddings, funerals, religious gatherings), physical surveillance of selected individuals, and financial flow monitoring within and across borders.
- Analysis: Deviation from individual and network baselines — not absolute thresholds — triggers escalation. Particular attention to international communication surges, financial transfers, travel bookings, increased charitable engagement, and consultation of reference materials.
Workforce Sampling in Civil Society Organizations (Timeline: 6–12 months pilot)
- Scope: Random selection of individuals from NGOs, political parties, charitable organizations, and advocacy groups — explicitly including those working on issues perceived as contrary to conservative religious positions.
- Method: Discreet background review and baseline behavioral profiling. No intrusive surveillance unless indicators warrant escalation.
- Purpose: Establish whether taqiyya-based infiltration is occurring, identify compromised organizations, and protect civil society from subversion that ultimately discredits legitimate reform efforts.
Intelligence Fallout Assessment
This methodology generates intelligence dividends that passive mosque surveillance cannot:
- Deep-Cover and Dark-Figure Exposure — Controlled provocations force hidden operators into measurable micro-behaviors. Even a single confirmed identification of an unknown operator justifies the entire program's resource expenditure.
- Network Mapping Beyond Mosques — Observing reactions across the organizational spectrum — religious, charitable, political, secular — reveals connections invisible to mosque-centric collection. An operator in a women's rights NGO who contacts someone in a charitable foundation who contacts someone abroad after a provocation traces a network that no mosque surveillance would detect.
- Civil Society Protection — Identifying infiltrated organizations protects legitimate reform movements from internal sabotage — an outcome that serves both security and governance interests.
- Analytical Culture Shift — The systematic inclusion of "impossible" targets in monitoring rosters forces DGST analysts to challenge assumptions and resist confirmation bias — a discipline that improves collection quality across all domains.
3. Religious Discourse Management: From Centralized Control to Monitored Pluralism
The Intelligence Problem
Following the 2003 Casablanca bombings, MEIA mandated centralized Friday khutbah (خطبة الجمعة) content — a direct security response. Two decades later, this policy has generated an intelligence paradox: uniform sermons create uniform blind spots. When every mosque delivers identical state-approved content, authentic congregational sentiments and imam views become invisible to collection. Dissenting views do not disappear; they migrate to unmonitored channels — private WhatsApp groups, family lifecycle events (عزاء), informal study circles, and encrypted social media platforms where DGST has minimal visibility.
Morocco's Islamic landscape — rooted in the Maliki rite (المذهب المالكي) and a historically pluralistic Sufi tradition under the Alawite monarchy's "Commander of the Faithful" (أمير المؤمنين) authority — is inherently resistant to homogenization. Foreign actors exploit this resistance. Pattern-consistent reporting suggests Qatar and Turkey fund Brotherhood-sympathetic networks through charitable fronts, while Saudi Arabia's post-MBS "moderated Wahhabism" competes for ideological influence. The UAE counters with parallel patronage streams.
Concrete indicators: Palestinian solidarity mobilizations (2023–2025) — including the 2025 Tangier port actions targeting Maersk shipments — were largely organized through informal channels and social media, not mosques, which had been rhetorically neutralized. The Palestinian issue retains unique mobilization power in Morocco, cutting across secular and religious lines; for religiously affiliated actors, it is framed as a religious obligation, amplifying its reach well beyond conventional political channels. DGST's mosque-focused collection is therefore monitoring the wrong surface.
How Discourse Reform Enables Intelligence
A tiered transition from uniform to locally responsive khutbahs transforms mosques from intelligence dead zones into real-time sentiment barometers. When imams address community-specific concerns within defined parameters, sermon content becomes direct, voluntary, organic self-reporting intelligence that no technical surveillance can replicate.
Operational Recommendations
Tiered Pluralism Implementation (Phase 1: 12 months)
- Tier 1 — National Framework (MEIA Central): Core theological guardrails: affirmation of monarchical religious authority, Maliki-Sufi boundaries, prohibitions on takfiri rhetoric, sectarian incitement, and calls to violence.
- Tier 2 — Regional Adaptation (Provincial MEIA Offices): Imams submit locally drafted khutbah outlines via a secure mobile application (developed with DGSN cybersecurity directorate) for review by trained regional panels (MEIA scholars + DGST liaison under civilian cover + community representative). Turnaround: 72-hour review cycle with veto authority on redline violations.
- Tier 3 — Community Responsiveness: Approved imams (24+ months compliance, positive feedback, DGST clearance) gain latitude for real-time topical response without prior submission. Content reviewed post-delivery via audio recording (framed as archival preservation).
App-Based Submission and Feedback System
- Imams submit outlines through secure portal; regional panels review using standardized rubric (theological compliance, tone, relevance, misinterpretation risk).
- Critical intelligence feature: Congregation feedback module — anonymous rating and concern flagging. Data flows directly into DGST analytical databases (content + sentiment dual-stream product).
- Precedent: Adapted from French colonial religious discourse review mechanisms with modern technology.
Imam Training Expansion
- Scale مدرسة محمد السادس للأئمة والمرشدين والمرشدات (Mohammed VI Institute) programs to cover 48,000 imams over three years.
- Curriculum additions:
- Security awareness module (DGST-developed): radicalization indicators, reporting channels, foreign import identification (framed as community safety).
- Advanced Maliki-Sufi theological argumentation to counter Salafi/Brotherhood narratives.
- Communications/counter-narrative skills: media literacy, social media engagement.
- Budget: MEIA sovereignty funds + Hassan II Fund allocation.
Operational Checklist
- MEIA launches secure app pilot (100 mosques).
- DGST embeds liaison in regional review panels (covert).
- Institute accelerates training cycle with security module.
- Post-khutbah: automated NLP analysis of audio/text + feedback data.
- Weekly DGST sentiment dashboard generation.
Intelligence Fallout Assessment
- Grievance Mapping in Real-Time — 15,000+ mosques delivering locally reflective sermons create a national sentiment map updated weekly. AI-powered NLP (Darija, MSA, Amazigh) detects thematic clustering, escalation, and foreign narrative adoption. Target: flagging shifts within 48–72 hours, compared to the current weeks-to-months lag.
- Clandestinity Reduction — Visible grievance expression in monitored spaces reduces migration to encrypted channels that DGST cannot penetrate. Every aired grievance is one fewer hidden in inaccessible Telegram groups.
- Foreign Influence Detection — DGED external funding reports (e.g., Turkish charitable spikes) cross-referenced with local sermon content shifts provide actionable evidence of influence ops impossible under uniform policy.
- Predictive Capability — Historical sermon–protest correlations enable I&W protocols (e.g., Gaza themes preceding mobilization). Target: 50% reduction in response time from indicator to operational assessment.
Metrics and Evaluation Criteria
| Indicator | Baseline | Target (24 months) | Data Source |
|---|---|---|---|
| Sermon local adaptation rate | 0% | 20% incorporating local themes | MEIA app analytics |
| Public trust in mosque discourse | Estimated 40–50% | 70% approval | Independent polling |
| Underground network detection | Reactive | Proactive 3+ networks/year | DGST case files |
| Foreign narrative adoption lag | Undetectable domestically | Flagged within 72 hours | NLP analysis system |
| Imam security-awareness completion | Near 0% | 60% of active imams | Mohammed VI Institute records |
Pilot: 100 mosques in tension-sensitive zones (Rif corridor, Beni Mellal-Khénifra, eastern border, Casablanca periphery).
4. Foreign Influence Operations: Disrupting External Vectors to Ease Domestic Collection
The Intelligence Problem
Morocco faces a multi-axis foreign influence environment straining DGST and DGED capacity. Principal vectors (pattern analysis, varying verification confidence):
- Qatar/Turkey: Funding Brotherhood networks via charities, education, media proxies — long-cycle youth/professional targeting.
- Saudi Arabia: Post-Vision 2030 moderated Wahhabism via scholarships, pilgrim facilitation — dilutes Maliki-Sufi coherence.
- UAE: Counter-Brotherhood patronage creating parallel networks.
- Algeria (medium confidence, unverified): Information ops using fabricated Moroccan personas to amplify corruption/prisoner/Sahrawi narratives — troll-farm exploitation.
Religious travel (Hajj, Umrah, diaspora visits) creates surveillance gaps exploitable for recruitment or ideological programming. Meanwhile, protests — the 2025 GenZ 212 movement, Gaza solidarity actions — incorporate externally amplified themes. Distinguishing organic grievance from manufactured agitation remains analytically challenging under the current reactive posture.
How Disrupting Foreign Vectors Enables Domestic Intelligence
Every foreign network disrupted at source eliminates domestic monitoring requirements. DGED neutralization of a Gulf-funded front frees DGST from tracking dozens of downstream beneficiaries — a compounding return on a single disruption.
Operational Recommendations
Integrated Agency Framework
DGED (External):
- Analytical cell for Gulf remittance/charitable tracking via Bank Al-Maghrib/UTRF.
- Enhanced liaison with European partners (DGSE, BND, CNI) for diaspora monitoring.
- Targeted disruption (legal sanctions, diplomatic pressure, covert penetration).
DGST (Internal):
- Receive DGED leads for domestic endpoint investigation.
- Expand technical collection on amplification networks (platform data requests under counter-terrorism law).
- Dedicated Algeria-focused IO tracking unit (Darija/Algerian dialect forensics).
Technology-Driven Detection Architecture
- Arabic NLP platform (MSA, Darija, Gulf dialects) for coordinated inauthentic behavior detection across X, Facebook, Instagram, TikTok, Telegram — target: 500+ accounts/year flagged.
- Travel pattern analysis: Integrate DGSN border data with DGED reporting — flag frequent Umrah, Qatar/Turkey layovers, post-travel thematic shifts.
Operational Checklist
- DGED establishes Gulf funding cell; shares weekly leads with DGST.
- DGST launches Algeria IO unit; procures NLP platform.
- Joint fusion cell operational (monthly assessment products).
- UTRF automated alerts for front-organization signatures.
- DGED-DGST joint travel anomaly protocol tested quarterly.
Intelligence Fallout Assessment
- Resource Liberation — Top 10 disrupted networks reduce domestic monitoring by ~25–30% (dozens of FTEs redeployed).
- Predictive Modeling — Funding–unrest correlations enable prepositioning (e.g., 60-day lead on northern protest cycles).
- Deterrence Effect — Demonstrated disruption raises adversary cost — ROI drops below sustained engagement threshold.
- Counter-Capability — Understanding adversary methods enables inoculation (counter-narrative campaigns without propaganda label).
Metrics and Evaluation Criteria
| Indicator | Baseline | Target (18 months) | Data Source |
|---|---|---|---|
| Foreign-funded networks disrupted | Ad hoc | 10+ per year | DGED/DGST joint reporting |
| Inauthentic accounts flagged | Minimal | 500/year assessed | Technical monitoring platform |
| DGST FTEs freed | 0 | 15–20 FTEs redeployed | DGST resource allocation |
| Travel anomalies investigated | Unknown | 100% of flagged within 30 days | DGSN/DGED integration |
| Cross-agency fusion products | Rare | Monthly | Inter-agency cell |
5. Gender and Education Dynamics: Defusing Resentment Before It Becomes a Recruitment Tool
The Intelligence Problem
Mudawana reforms (مدونة الأحوال الشخصية) — expanding women's rights — are essential modernization but create an intelligence-relevant pressure point. Women hold 51.6% of tertiary enrollment and achieve higher pass rates, yet face persistent cultural and labor-market barriers. Male youth unemployment (35–40% for 15–24) creates a large, frustrated demographic vulnerable to radicalization.
Unverified but concerning perceptions: public-sector hiring favors women as "gifts" — the perception itself is the threat vector, feeding narratives of male marginalization exploited by Brotherhood/Salafi recruiters. Gender resentment propagates through private social networks that intersect with foreign operations and radicalization nodes.
How Addressing Gaps Enables Intelligence
Reducing legitimate grievance shrinks adversary recruitment pools. Fewer susceptible individuals = fewer DGST monitoring targets, fewer interdiction requirements, fewer radicalization incubators.
Operational Recommendations
Educational Intervention Program
- Lead: Ministry of National Education + DGST advisory targeting.
- Male Engagement: Commission boys' disengagement study; implement mentoring (role models from security/professional sectors), vocational pathways (20% enrollment increase target), after-school programs in high-risk neighborhoods.
Hiring Transparency Mechanisms
- Public sector: Publish job criteria, scoring, anonymized statistics on centralized portal.
- Private sector: Tax incentives via CGEM for voluntary transparency.
Integrated Societal Messaging
- Frame reforms as shared prosperity via mosques (MEIA khutbahs on family solidarity), schools (media literacy curricula), media (organic content partnerships).
Operational Checklist
- Education Ministry commissions disengagement study (Q1).
- Launch mentoring/vocational pilots in tension zones (Q2).
- Hiring portal live (Q3).
- MEIA integrates equity themes into pluralism khutbahs.
- DGST monitors resentment narrative volume quarterly.
Intelligence Fallout Assessment
- Recruitment Pool Reduction — 15–20% susceptible population drop = proportional DGST queue reduction.
- Social Media Noise Reduction — Lower organic resentment = clearer foreign signal detection.
- Counter-Amplification Targeting — Domestic data debunks foreign claims → DGED/DGST closed-loop defensive ops.
- Early Warning HUMINT — School/mentoring channels create trusted reporting points for radicalization indicators.
Metrics and Evaluation Criteria
| Indicator | Baseline | Target (24 months) | Data Source |
|---|---|---|---|
| Male vocational enrollment | Current | +20% | Ministry of Education |
| Youth unemployment (15–24, male) | 35–40% | 30% (5–10 point drop) | HCP statistics |
| Gender bias perception | High | 50% reduction | Independent polling |
| Gender-themed radicalization spikes | Frequent | 40% volume reduction | DGST monitoring |
| School-based early warning reports | Near zero | Established quarterly channel | Ministry/DGST liaison |
6. Integrated Assessment: The Intelligence Architecture of Proactive Reform
Connecting the Domains
Action in one domain generates dividends across all:
- Mosque renovation creates infrastructure for discourse monitoring.
- Provocation-and-observe methodology flushes hidden operators across mosques, civil society, and political organizations — feeding all other collection streams.
- Pluralism generates sentiment data revealing foreign penetration.
- Foreign disruption reduces amplification of gender/education resentment.
- Gender/education reform shrinks recruitment pool gravitating to independent mosques.
Cumulative effect: compounding threat reduction and collection expansion across all domains.
Cross-Agency Operational Architecture
| Function | DGST Role | DGED Role | Supporting Agencies |
|---|---|---|---|
| Mosque infrastructure | Domestic monitoring, community liaison | Foreign ideology import tracking | MEIA, Land Use Planning |
| Surveillance illusion / hidden operators | Provocation design, roster management, civil society sampling | International comms and travel monitoring | UTRF, Bank Al-Maghrib, MEIA |
| Religious discourse | Sermon analysis, imam source development | External funding correlation | MEIA, Mohammed VI Institute |
| Foreign influence | Domestic endpoint investigation | Source-country disruption, tracking | UTRF, DGSN, Bank Al-Maghrib |
| Gender/education | Radicalization indicators | Foreign amplification detection | Education, Solidarity |
Budget and Resourcing Framework
- Mosque pilot (Year 1): MAD 296M rehab fund + MEIA modernization. Additional: MAD 50M tech integration (50 sites).
- Discourse reform (Years 1–3): MEIA funds (MAD 10M app, MAD 80M training). ROI: 2–3 FTE savings/mosque.
- Foreign counter-ops: DGED budget (classified). Tech platform: MAD 30M NLP system.
- Education/gender: Education reallocation + Hassan II Fund. MAD 200M over 24 months.
Strategic Timeline
| Phase | Period | Priority Actions |
|---|---|---|
| Immediate | Months 1–6 | Mosque audits; discourse pilot (100 mosques); NLP platform procurement; education study |
| Consolidation | Months 6–18 | Renovation execution; imam training acceleration; DGED-DGST fusion cell; hiring portal |
| Scaling | Months 18–36 | National pluralism rollout; predictive analytics; educational scale-up; metrics review |
Final Assessment
Morocco possesses the institutional architecture, intelligence capability, and societal resilience required. Societal investment is intelligence investment. Every dirham spent on mosque safety, imam training, foreign disruption, and youth opportunity generates returns in stability, prosperity, and operational currency: better collection, faster warning, more effective preemption.
The I&W framework demands action on probability, not certainty. The patterns identified meet the threshold for proactive engagement. Morocco's security services must integrate efforts across these domains now, converting vulnerabilities into intelligence advantages.
Umbrax specializes in North African intelligence architecture and MENA threat assessment. SecurityNak publishes in English and French.
The assessments represent judgments based on open-source information, pattern analysis, and unverified but credible reporting. Confidence levels vary by claim. Readers in policy/intelligence positions should treat accordingly.